Vulnerabilities of Volkswagen and Audi Cars to Remote Hacking
Remote Hacking
A cyber-security firm in the Netherlands has discovered that the in-vehicle infotainment (IVI) systems deployed with some car models from the Volkswagen Group are vulnerable to remote hacking.
Researchers in security with Computest said they successfully tested their findings and exploit chains on Volkswagen Golf GTE and Audi A3 Sportback e-tron models (Audi is a brand part of the Volkswagen Group). Basically, they hacked the cars with just a wifi connection.
The company successfully used the car's WiFi connection to exploit an exposed port and gain access to the car's IVI, which is manufactured by the electronics company Harman. This allowed the researchers to access other important car data.
"Under certain conditions, attackers could listen in to conversations the driver is conducting via a car kit, turn the microphone on and off, as well as gaining access to the complete address book and the conversation history," Computest researchers said.
"Furthermore, due to the vulnerability, there is the possibility of discovering through the navigation system precisely where the driver has been, and to follow the car live wherever it is at any given time," researchers added.
The researchers found they could have exploited the systems more but stopped short as the IVI system is also indirectly connected to the car's acceleration and braking system. The reason they stopped investigating the possibility of interacting with those systems is that they feared breaching Volkswagen's intellectual property.
The security company also discovered other flaws that could be exploited via USB debugging ports located under the car dashboard. All these flaws were discovered in July 2017, and the security company reported all the issues to Volkswagen, even participating in meetings with the car maker.
"The vulnerability we initially identified should have been found during a proper security test," researchers said. "During our meeting with Volkswagen, we had the impression that the reported vulnerability and especially our approach was still unknown. We understood in our meeting with Volkswagen that, despite it being used in tens of millions of vehicles worldwide, this specific IVI system did not undergo a formal security test and the vulnerability was still unknown to them."
Even though Volkswagen deployed an untested system within its cars, they worked with the research team to address the reported flaws. 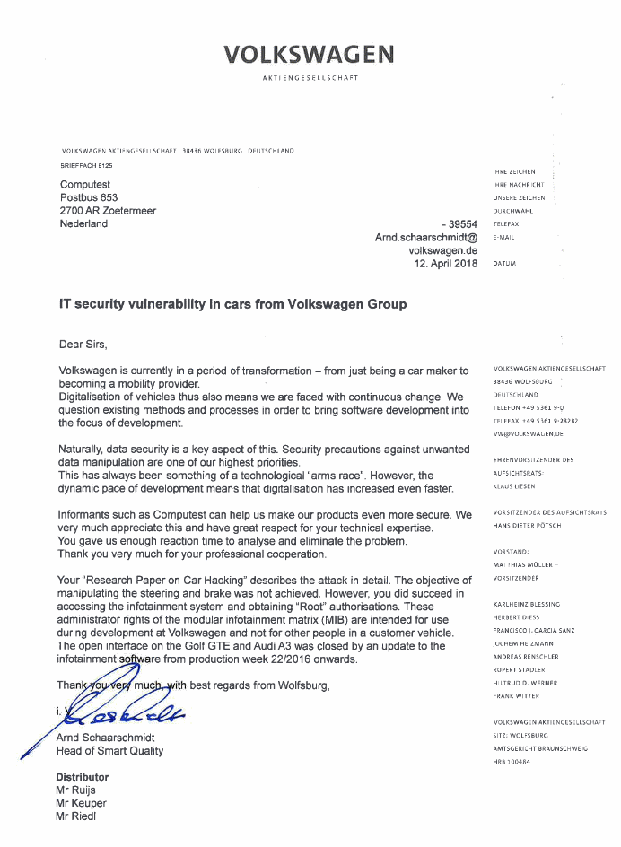
"The open interface on the Golf GTE and Audi A3 was closed by an update to the infotainment software from production week 22/2016 onwards," Volkswagen execs wrote in a letter sent to Computest, shared by the researchers.
Researchers, though are still quite worried about the security vulnerabilities with Volkswagen IVI systems as they did not come with an over-the-air update, meaning it couldn't be updated with a software patch from afar.
In conversations with Volkswagen, researchers found out that flaws were being eliminated in infotainment systems still in production, but researchers are worried that there is no plan to deal with cars already sold to customers.
For their part, researchers made it very clear they don't plan to reveal the exact services and ports they used to break into the VW Golf and Audi A3 models during their experiments. Computest researcher wrote in a technical paper.
"When writing this paper, we decided to not provide a full disclosure of our findings. We describe the process we followed, our attack strategy and the system internals, but not the full details on the remote exploitable vulnerability as we would consider that being irresponsible,"
"This might disappoint some readers, but we are fully committed to a responsible disclosure policy and are not willing to compromise on that.
"We think that giving full disclosure could put people at risk, while not adding much to this paper"
In August 2016, Volkswagen fixed another major security flaw in its keyfob system that affected almost all models sold in the past 20 years. 
Author

Justin Kavanagh
Justin Kavanagh is a recognised leader
in automotive intelligence and vehicle
data supply to the entire motor industry.
He has almost 20 years experience in
building systems from the ground up.
As the Managing Director of Vehicle
Management System, he understands the
need and importance of trustworthy and
reliable vehicle history and advice to
both the trade and the public.
Follow me on LinkedIn
